VR Hardware Security: Protecting Your Devices from Cyber Threats in 2026

VR Hardware Security: Best Practices for Protecting Your Devices from Cyber Threats in 2026 Across the US (INSIDER KNOWLEDGE)
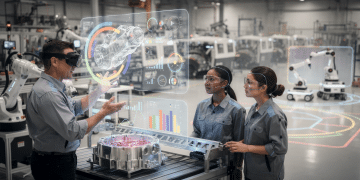
The dawn of 2026 brings with it an unprecedented surge in virtual reality (VR) adoption, extending far beyond entertainment into critical sectors like healthcare, education, manufacturing, and defense. As VR headsets and associated hardware become more sophisticated and integrated into our daily lives, the imperative for robust VR hardware security has never been more urgent. Cybercriminals, always quick to exploit new vulnerabilities, are increasingly targeting these devices, recognizing them as gateways to sensitive personal and corporate data, intellectual property, and even operational control. This comprehensive guide will delve into the critical aspects of protecting your VR hardware from the ever-evolving landscape of cyber threats in 2026, offering insider knowledge and actionable best practices for users across the United States.
The immersive nature of VR means that a breach isn’t just a data leak; it can compromise your physical environment, identity, and even psychological well-being. Imagine a compromised VR system used in a surgical simulation, a military training exercise, or for sensitive corporate collaboration. The implications are staggering. Therefore, understanding and implementing stringent VR hardware security measures is no longer optional but a fundamental requirement for anyone engaging with this transformative technology.
The Evolving Threat Landscape for VR Hardware in 2026
In 2026, cyber threats targeting VR hardware have become more sophisticated and multi-faceted. Gone are the days of simple malware. We’re now contending with highly targeted attacks, leveraging advanced persistent threats (APTs), supply chain compromises, and even physical tampering. Understanding these evolving threats is the first step towards building an impregnable defense for your VR hardware security.
Here is a video that you may find helpful:
Advanced Persistent Threats (APTs) in VR
APTs are no longer exclusive to nation-state espionage or large corporations. They are increasingly being deployed against high-value individual targets and smaller enterprises using VR for sensitive operations. These attackers gain unauthorized access to VR systems and maintain a prolonged, undetected presence to steal data or disrupt operations. For VR hardware, this could mean embedding malicious firmware during manufacturing, exploiting zero-day vulnerabilities in VR operating systems, or even using social engineering to trick users into installing compromised applications. The goal is often to exfiltrate biometric data, financial information, or intellectual property accessed within the VR environment.
Supply Chain Attacks on VR Hardware
The global supply chain for VR hardware is complex, involving numerous manufacturers, component suppliers, and distributors. Each link in this chain presents a potential vulnerability. Cybercriminals can inject malicious code or hardware components at various stages, from the initial design and manufacturing of chips to the assembly of the final device. By the time the VR headset reaches the end-user, it could already be compromised. This makes verifying the integrity of your VR hardware, from purchase to deployment, a critical aspect of VR hardware security.
Physical Tampering and Side-Channel Attacks
While often overlooked in the digital age, physical security remains paramount for VR hardware. An attacker with physical access to a VR device can perform various nefarious acts, including installing spyware, extracting sensitive data directly from memory, or even modifying hardware components. Side-channel attacks, which analyze physical emissions from the device (like power consumption or electromagnetic radiation) to infer cryptographic keys or other sensitive information, are also becoming more practical with specialized equipment. This emphasizes the need for secure storage and monitoring of VR devices, especially in enterprise settings.
Data Exfiltration and Privacy Concerns
VR devices collect an immense amount of data: head movements, eye-tracking, gaze direction, hand gestures, voice commands, and even biometric data. This data, if compromised, can reveal highly personal insights about users, their habits, and their environments. Beyond personal privacy, corporate VR applications often handle confidential designs, prototypes, and strategic plans. The exfiltration of such data can lead to significant financial losses, reputational damage, and competitive disadvantage. Protecting this data is a core component of effective VR hardware security.
Best Practices for Robust VR Hardware Security in 2026
Now that we’ve outlined the threats, let’s dive into the actionable best practices for fortifying your VR hardware security in 2026. These recommendations span across device selection, configuration, usage, and ongoing maintenance.
1. Secure Device Procurement and Authentication
The journey to secure VR hardware begins even before you unbox the device. In 2026, organizations and individuals must be vigilant about where and how they acquire VR equipment.
- Purchase from Reputable Vendors: Always buy VR hardware directly from authorized manufacturers or their certified resellers. Avoid grey markets or suspiciously cheap deals, as these are often avenues for compromised devices.
- Verify Device Integrity: Upon receipt, implement procedures to verify the device’s authenticity. This could involve checking unique serial numbers against manufacturer databases, inspecting packaging for signs of tampering, and even using forensic tools for advanced integrity checks before initial deployment, especially for enterprise-grade hardware.
- Secure Boot and Trusted Platform Modules (TPMs): Modern VR hardware should come equipped with secure boot capabilities and TPMs. Secure boot ensures that only trusted software can load during startup, preventing rootkits and other low-level malware. TPMs provide hardware-based cryptographic functions and secure storage for keys and measurements, significantly enhancing the device’s overall security posture. Always ensure these features are enabled and properly configured.
2. Implement Strong Access Controls and Authentication
Access to VR devices and the data they contain must be tightly controlled. In a multi-user environment, this becomes even more critical.
- Multi-Factor Authentication (MFA): Where available, enable MFA for VR headset logins and associated accounts. This could involve biometrics (fingerprint, facial recognition, or even eye-tracking patterns), hardware tokens, or authenticator apps. Passwords alone are no longer sufficient.
- Biometric Security: Leverage the biometric capabilities of advanced VR headsets. Eye-tracking for user authentication or unique hand gesture patterns can provide an additional layer of security, creating a more seamless yet secure login experience.
- Role-Based Access Control (RBAC): For enterprise VR deployments, implement RBAC. Users should only have access to the VR applications and data necessary for their specific roles. This minimizes the blast radius in case of a compromise.
- Secure User Profiles: Ensure that individual user profiles on shared VR devices are securely compartmentalized to prevent cross-contamination of data or unauthorized access between users.

3. Regular Software and Firmware Updates
Software vulnerabilities are a primary vector for cyberattacks. Keeping your VR hardware’s operating system, applications, and firmware up-to-date is non-negotiable for robust VR hardware security.
- Automate Updates: Configure VR devices to automatically download and install updates from trusted sources whenever possible.
- Monitor for Patches: Regularly check manufacturer websites and security advisories for critical patches and firmware updates. Apply these promptly, especially those addressing known vulnerabilities.
- Verify Update Authenticity: Be wary of unofficial updates or those from unknown sources, as these can be laced with malware. Always verify the digital signature of updates if possible.
4. Network Security for VR Devices
VR devices are increasingly connected, making network security a vital component of VR hardware security.
- Dedicated and Segmented Networks: In enterprise settings, consider placing VR devices on a dedicated and segmented network (VLAN) separate from critical corporate infrastructure. This limits lateral movement for attackers.
- Strong Wi-Fi Encryption: Ensure all Wi-Fi networks used by VR devices employ strong encryption protocols, such as WPA3. Avoid public or unsecured Wi-Fi networks for sensitive VR activities.
- Firewall Configuration: Configure firewalls to restrict outbound and inbound traffic for VR devices to only necessary ports and protocols. Implement intrusion detection/prevention systems (IDS/IPS) to monitor for suspicious network activity.
- VPN Usage: For remote access to corporate VR resources or when using VR in untrusted network environments, utilize a Virtual Private Network (VPN) to encrypt all traffic.
5. Data Encryption and Privacy Controls
Protecting the data generated and processed by VR hardware is paramount.
- Full Disk Encryption: Ensure that the internal storage of your VR headset is encrypted. This protects data at rest in case the device is lost or stolen.
- In-Transit Encryption: All data transmitted to and from the VR device (e.g., to cloud services, other devices) should be encrypted using protocols like TLS/SSL.
- Privacy Settings Configuration: Regularly review and configure the privacy settings on your VR device and associated applications. Limit data collection to what is strictly necessary and understand what data is being shared with third parties. Be especially cautious with permissions for microphones, cameras, and location services.
- Data Minimization: Only collect and store data absolutely required for the VR application’s function. The less sensitive data stored, the less there is to lose in a breach.
6. Secure Application Management
Applications are a common entry point for malware. Exercise extreme caution when installing VR applications.
- App Store Vigilance: Only download VR applications from official, reputable app stores (e.g., Meta Quest Store, SteamVR, Pico Store). Avoid sideloading apps from unknown sources unless absolutely necessary and after thorough vetting.
- Permission Review: Before installing an app, carefully review the permissions it requests. Does a VR game really need access to your contacts or full network control? If permissions seem excessive, reconsider installation.
- Regular App Audits: Periodically review the applications installed on your VR device and uninstall any that are no longer used or seem suspicious.
- Application Sandboxing: Modern VR operating systems should ideally employ application sandboxing, isolating apps from each other and the core system to limit the damage a malicious app can cause.

7. Physical Security and Asset Management
Don’t underestimate the importance of physical security for your VR hardware security.
- Secure Storage: When not in use, store VR devices in a physically secure location, especially in enterprise environments. Consider locked cabinets or rooms with access controls.
- Asset Tagging and Inventory: Maintain an accurate inventory of all VR hardware, including serial numbers and assigned users. This aids in tracking and recovery in case of loss or theft.
- Tamper Detection: For high-security environments, consider physical tamper-evident seals or sensors on VR hardware that can alert administrators to unauthorized access attempts.
- Device Wiping Procedures: Establish clear procedures for securely wiping data from VR devices before disposal, repurposing, or returning them to a manufacturer. Standard factory resets may not be sufficient to erase all sensitive data.
8. User Education and Awareness
The human element remains the weakest link in any security chain. Educating VR users is paramount.
- Phishing and Social Engineering Training: Train users to recognize phishing attempts, especially those targeting VR accounts or promising exclusive VR content. Social engineering attacks designed to gain access to VR hardware are on the rise.
- Password Hygiene: Emphasize the importance of strong, unique passwords for all VR-related accounts and the use of password managers.
- Reporting Suspicious Activity: Encourage users to report any unusual behavior from their VR device, unexpected app installations, or performance issues that might indicate a compromise.
- Privacy Best Practices: Educate users on the types of data collected by VR devices and the importance of configuring privacy settings correctly.
9. Endpoint Detection and Response (EDR) for VR
As VR systems become more akin to traditional computing endpoints, traditional security solutions are adapting. In 2026, specialized EDR solutions for VR are emerging.
- Behavioral Monitoring: EDR for VR can monitor the behavior of VR applications and the VR operating system for anomalies that might indicate malicious activity.
- Threat Intelligence Integration: Integrate VR EDR with broader threat intelligence platforms to quickly identify and respond to emerging VR-specific threats.
- Automated Response: Implement automated response mechanisms to isolate compromised VR devices, terminate malicious processes, or trigger alerts for security teams.
10. Regular Security Audits and Penetration Testing
No security posture is perfect. Regular testing is essential to identify weaknesses and ensure your VR hardware security measures are effective.
- Vulnerability Assessments: Conduct periodic vulnerability assessments of your VR hardware, software, and network configurations to identify potential weaknesses.
- Penetration Testing: Engage ethical hackers to perform penetration tests on your VR ecosystem. These ‘red team’ exercises can simulate real-world attacks and uncover vulnerabilities before malicious actors do.
- Compliance Audits: For organizations, ensure your VR deployments comply with relevant industry regulations and data protection laws (e.g., HIPAA, GDPR, CCPA).
The Future of VR Hardware Security: What to Expect Beyond 2026
The pace of innovation in VR is relentless, and so too is the evolution of cyber threats. Looking beyond 2026, we can anticipate several key trends that will shape the future of VR hardware security:
- Hardware-Level Security Enhancements: Expect more sophisticated hardware-based security features, including advanced secure enclaves, physically unclonable functions (PUFs), and integrated quantum-resistant cryptography directly into VR chips.
- AI and Machine Learning for Threat Detection: AI and ML will play an increasingly critical role in real-time threat detection and anomaly identification within VR environments, capable of recognizing subtle deviations in user behavior or system performance that indicate a compromise.
- Decentralized Identity and Blockchain Integration: Blockchain technology could offer decentralized identity management for VR users, providing enhanced privacy and control over personal data, mitigating risks associated with centralized identity providers.
- Standardization and Regulation: As VR becomes more ubiquitous, expect greater standardization of security protocols and potentially more stringent regulatory oversight for VR hardware and software, especially in critical sectors.
- Enhanced Biometric Authentication: Beyond simple eye-tracking, future VR systems might incorporate more advanced biometric authentication methods, such as brainwave patterns or unique physiological responses, offering even more robust identity verification.
The integration of these advanced security measures will be crucial in ensuring that VR can achieve its full potential without compromising user trust or organizational integrity. The industry, from hardware manufacturers to software developers and end-users, must collectively commit to prioritizing security from design to deployment.
Conclusion: A Proactive Stance on VR Hardware Security is Key
The immersive capabilities of virtual reality promise a future of unparalleled experiences and transformative applications. However, this future can only be realized if the underlying hardware is secure. In 2026, the threats to VR hardware security are real, diverse, and constantly evolving. From sophisticated APTs and supply chain compromises to physical tampering and pervasive data privacy concerns, the challenges are significant.
By adopting a proactive and multi-layered security strategy, individuals and organizations can significantly mitigate these risks. This includes diligent procurement, robust access controls, continuous updates, strong network security, comprehensive data encryption, secure application management, unwavering physical security, and, critically, ongoing user education. The insider knowledge shared here emphasizes that security is not a one-time fix but an ongoing commitment.
As VR continues its rapid ascent, prioritizing VR hardware security will not only protect your devices and data but also foster the trust necessary for the widespread and safe adoption of this revolutionary technology across the United States and beyond. Stay vigilant, stay informed, and stay secure in the metaverse of 2026.